Outsourcing and Security Risks
Outsourcing business services to a third-party provider might present risk to your organization’s security, reputation, and regulatory compliance. Sound third-party risk management is the answer.

Vulnerabilities in Hybrid Work Environments
Hybrid work, SD-WAN, and digital-first adoption make enterprises more vulnerable to attack, increasing the need for SSE solutions, the company says.
Challenges in Cybersecurity
New court filings expose allegations of the communications authority claiming cyber attack was carried out "through a simple process of trial and error.” Swatting is a form of criminal harassment in which attackers “prank call” law enforcement to trick police into surrounding unsuspecting homes — and the resulting confrontations can go very badly.

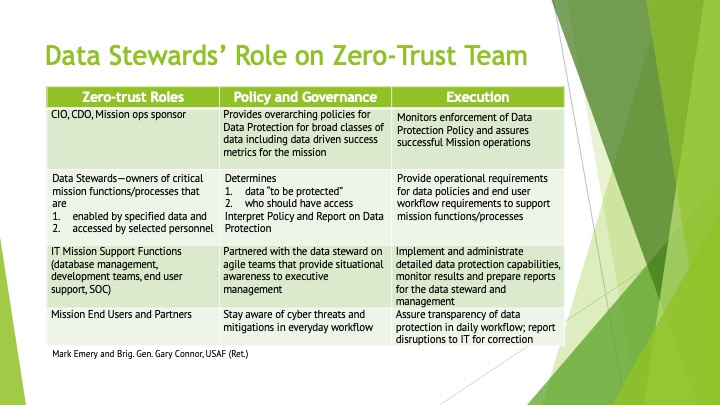
Implementing Zero Trust Strategy
Getting the basics right to ensure a successful zero trust strategy. The ruling means the litigation — which began in 2020 — can continue. The case involves whether cookies collecting user information violates GDPR and whether the two companies are responsible for what web site operators do.
Continuous Monitoring for Security
With Sonaris, an internally developed tool, AWS continuously monitors its systems to pre-empt attacks on customer data. Business communications fall under the scope of the controversial European Union chat surveillance bill.
Security Breaches and Investigations
Well-known zero-click spyware vendor NSO Group admits to widespread use of Pegasus. AMD is investigating the alleged data breach threatening to expose sensitive employee and customer information, along with other proprietary data. Expect only a short-term reduction in attacks on enterprises from the group, warns former FBI agent.
Advancing in Cybersecurity
The Certified Cloud Security Professional (CCSP) is a cloud-focused security credential that can advance your career as a cybersecurity pro. Here are the details you need to know. The Irish Data Protection Commission asked Meta to delay training its AI on data from users in the European Union.
Secure Procurement of SaaS Solutions
Companies looking to use SaaS solutions should involve the security team in the procurement process and pay attention to contract language. This podcast series brought to you by Microsoft and IDG, will explore the core components of a modern security strategy, with insights and tips from leading security experts. We’ll discuss how ongoing and ever-changing threats, a growing security stack, and a shift to remote work make it difficult for CISOs and their security teams to balance enterprise-grade security with end-user productivity.