SMBs are being hit by malicious productivity tools – Zoom and more
Recent research from Russian cybersecurity firm Kaspersky has revealed a concerning trend in cyberattacks targeting small and medium-sized businesses. According to the study, there has been a 115% increase in cyberattacks mimicking popular productivity apps like Zoom and AI tools in 2025.
Exploiting Popular Tools
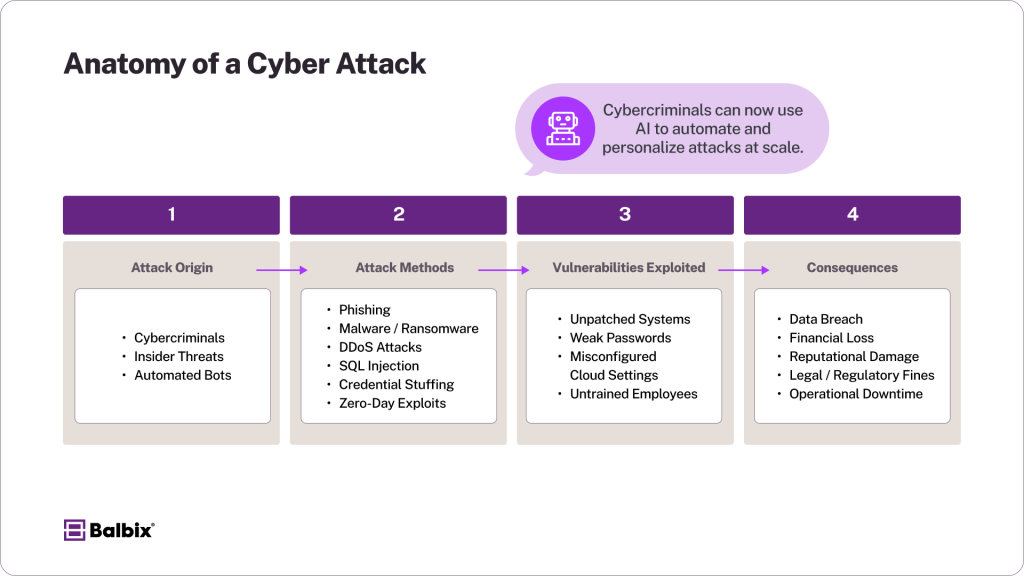
The analysis conducted by Kaspersky identified that cybercriminals are using fake productivity apps and AI tools to target unsuspecting businesses. Among the commonly impersonated apps were Zoom, Microsoft Office, ChatGPT, and DeepSeek. These attackers utilize phishing and spam campaigns to deceive users, often by offering fake deals or impersonating reputable brands to steal sensitive data or distribute malware.

Security expert Vasily Kolesnikov highlighted that cybercriminals tend to exploit the popularity and hype surrounding certain tools to trick users. The more attention a tool receives, the more likely it is that cybercriminals will create fake versions to lure in victims.
Increasing Threats
Kaspersky's findings indicated a significant rise in fake Zoom-related files in 2025, with Google Drive and Teams also experiencing increases in malicious files. Various Microsoft apps, such as Outlook, PowerPoint, Excel, Word, and Teams, were targeted in these attacks, with a notable portion of the attacks being observed by Kaspersky.

As a precautionary measure, Kaspersky advises businesses to establish clear protocols for software adoption and to define access rules for emails, cloud services, and other critical documents. Regularly backing up data can also serve as a reliable safeguard in the event of a cybersecurity breach.
Kolesnikov emphasized the importance of verifying the authenticity of links in suspicious emails to avoid falling victim to phishing schemes or unknowingly downloading harmful software.
It is crucial for businesses to remain vigilant and stay informed about the evolving tactics used by cybercriminals to protect their valuable data and assets.
Stay updated with the latest news, expert insights, and valuable resources for your business by subscribing to the TechRadar Pro newsletter.










